Understanding/Modifying Oracle GoldenGate Microservices Settings
Oracle GoldenGate Microservices provide a wide range of options from administration and security to enhance the replication setup and experience. The Microservices architecture makes interaction with Oracle GoldenGate much easier compared to the traditional Classic architecture. This architecture provides you with not one but four avenues to interact with GoldenGate to ensure replication is configured, started, stopped, and/or decommissioned. These avenues are:
- HTML5 Web Pages
- AdminClient (new command line tool)
- REST API
- PL/SQL
Now that you understand the four (4) ways to interact with Oracle GoldenGate Microservices, lets focus in on how this archtiecture actually works. Many people will immediatly access Oracle GoldenGate through the HTML5 Web Pages, but how is this tied to Microservices?
In order to understand this and to help in configuring additional behind the scene settings, Oracle has pushed out a utility called oggServiceConfig. This utiity is not currently bundled with the releases, but can be found with the our docker configuration files. This utility also allows you review your Microservices configuration; making this very useful in many different situations.
oggServiceConfig
Once you download the file, you will notice that it is written in python. You will need to make sure that python is avaliable on the machine where it will be ran. In my case, I’m running it on my MacBook and will be connecting to the Oracle GoldenGate environment via REST calls. Take a look at the file prior to running, there are a lot of great examples include.
You can do things like review/change the number of threads used by a service and review/modify the encryption ciphers that are used by a deployment after it is deployed. This is a really valuable tool.
To run the oggServiceConfig utility, here is an example:
$ python ./oggServiceConfig https://locahost:16000 Atlanta adminsrvr —user oggadmin —password ********
The corresponding output is:
Current value of "/" for "Atlanta/adminsrvr" is { "authorizationDetails": { "common": { "allow": [ "Digest", "x-Cert", "Basic" ] } }, "authorizationEnabled": true, "legacyProtocolEnabled": true, "network": { "serviceListeningPort": 16001 }, "security": true, "securityDetails": { "network": { "common": { "id": "OracleSSL" }, "inbound": { "cipherSuites": [ "TLS_RSA_WITH_AES_128_CBC_SHA256", "TLS_RSA_WITH_AES_128_GCM_SHA256", "TLS_RSA_WITH_AES_256_CBC_SHA256", "TLS_RSA_WITH_AES_256_GCM_SHA384", "TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256", "TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256", "TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384", "TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384", "TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256", "TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256", "TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384", "TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384", "TLS_DHE_RSA_WITH_AES_128_CBC_SHA256", "TLS_DHE_RSA_WITH_AES_128_GCM_SHA256", "TLS_DHE_RSA_WITH_AES_256_CBC_SHA256", "TLS_DHE_RSA_WITH_AES_256_GCM_SHA384", "TLS_ECDH_ECDSA_WITH_AES_128_CBC_SHA256", "TLS_ECDH_ECDSA_WITH_AES_128_GCM_SHA256", "TLS_ECDH_ECDSA_WITH_AES_256_CBC_SHA384", "TLS_ECDH_ECDSA_WITH_AES_256_GCM_SHA384", "TLS_ECDH_RSA_WITH_AES_128_CBC_SHA256", "TLS_ECDH_RSA_WITH_AES_128_GCM_SHA256", "TLS_ECDH_RSA_WITH_AES_256_CBC_SHA384", "TLS_ECDH_RSA_WITH_AES_256_GCM_SHA384" ], "crlEnabled": false, "protocolVersion": "1_2", "role": "server", "wrl": "file:/opt/app/oracle/gg_deployments/Atlanta/etc/ssl/OGG19C", "wrlPassword": "" }, "outbound": { "authMode": "client_server", "crlEnabled": false, "role": "client", "wrl": "file:/opt/app/oracle/gg_deployments/Atlanta/etc/ssl/DistroClient", "wrlPassword": "" } } }, "taskManagerEnabled": true, "workerThreadCount": 24
Now let’s change the number of threads that the Administration Service is going to use. Currently it is set to 24. Since I’m on a smaller machine … a virtual box image, I’m dong to reduce the threads to 10. Being on a smaller box, this should help reduce the resources I need, but 24 threads is correct for most production environments.
In order to change the value of workerThreadCount, you would do something similar to this:
$ python ./oggServiceConfig https://localhost:16000 Atlanta adminsrvr —user oggadmin —password ******** —path /workerThreadCount —value 5
The resulting output is:
Current value of “/workerThreadCount” for “Atlanta/adminsrvr” is 24. Setting new value and restarting service. New value of “/workerThreadCount” for “Atlanta/adminsrvr” is 5
Then you can check to verify that the setting has been changed:
$ python ./oggServiceConfig https://<a href="http://localhost:16000/" target="_blank" rel="noopener">localhost:16000</a> Atlanta adminsrvr —user oggadmin —password ****** Current value of "/" for "Atlanta/adminsrvr" is { "authorizationDetails": { "common": { "allow": [ "Digest", "x-Cert", "Basic" ] } }, "authorizationEnabled": true, "legacyProtocolEnabled": true, "network": { "serviceListeningPort": 16001 }, "security": true, "securityDetails": { "network": { "common": { "id": "OracleSSL" }, "inbound": { "cipherSuites": [ "TLS_RSA_WITH_AES_128_CBC_SHA256", "TLS_RSA_WITH_AES_128_GCM_SHA256", "TLS_RSA_WITH_AES_256_CBC_SHA256", "TLS_RSA_WITH_AES_256_GCM_SHA384", "TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256", "TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256", "TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384", "TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384", "TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256", "TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256", "TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384", "TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384", "TLS_DHE_RSA_WITH_AES_128_CBC_SHA256", "TLS_DHE_RSA_WITH_AES_128_GCM_SHA256", "TLS_DHE_RSA_WITH_AES_256_CBC_SHA256", "TLS_DHE_RSA_WITH_AES_256_GCM_SHA384", "TLS_ECDH_ECDSA_WITH_AES_128_CBC_SHA256", "TLS_ECDH_ECDSA_WITH_AES_128_GCM_SHA256", "TLS_ECDH_ECDSA_WITH_AES_256_CBC_SHA384", "TLS_ECDH_ECDSA_WITH_AES_256_GCM_SHA384", "TLS_ECDH_RSA_WITH_AES_128_CBC_SHA256", "TLS_ECDH_RSA_WITH_AES_128_GCM_SHA256", "TLS_ECDH_RSA_WITH_AES_256_CBC_SHA384", "TLS_ECDH_RSA_WITH_AES_256_GCM_SHA384" ], "crlEnabled": false, "protocolVersion": "1_2", "role": "server", "wrl": "file:/opt/app/oracle/gg_deployments/Atlanta/etc/ssl/OGG19C", "wrlPassword": "" }, "outbound": { "authMode": "client_server", "crlEnabled": false, "role": "client", "wrl": "file:/opt/app/oracle/gg_deployments/Atlanta/etc/ssl/DistroClient", "wrlPassword": "" } } }, "taskManagerEnabled": true, "workerThreadCount": 5 }
Hopefully, this sheds some light on how a running Oracle GoldenGate Microservice service can be modified (if needed) to meet some the changing needs in a configuration once it is established.
Enjoy!!
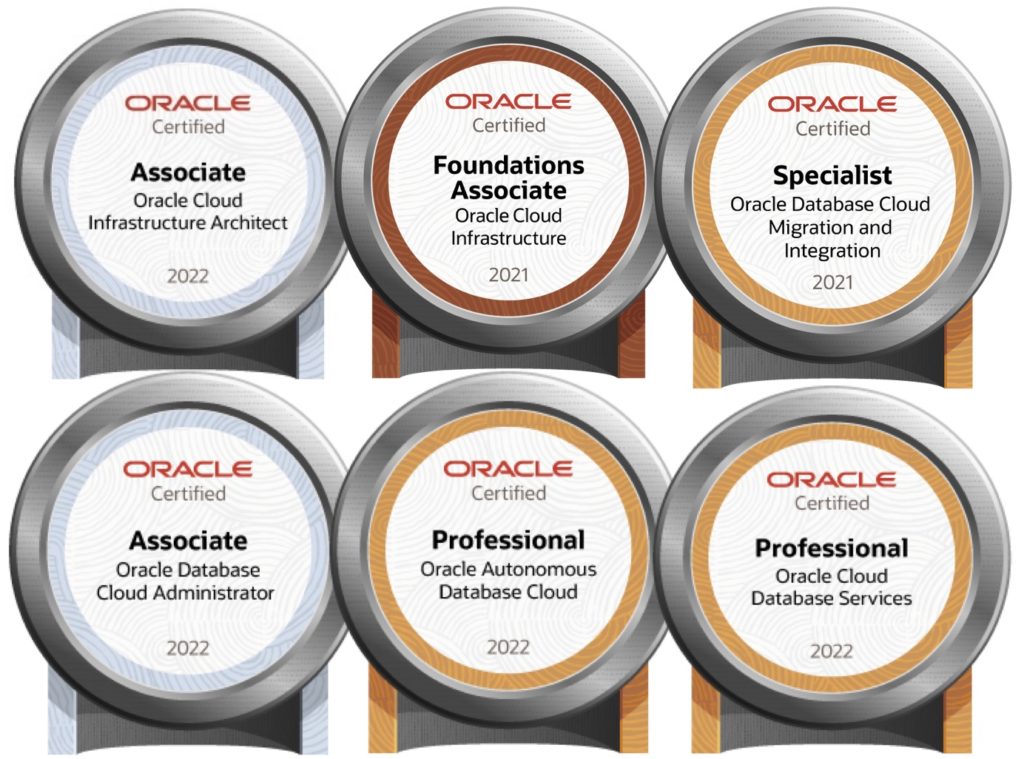
Current Oracle Certs
Bobby Curtis

I’m Bobby Curtis and I’m just your normal average guy who has been working in the technology field for awhile (started when I was 18 with the US Army). The goal of this blog has changed a bit over the years. Initially, it was a general blog where I wrote thoughts down. Then it changed to focus on the Oracle Database, Oracle Enterprise Manager, and eventually Oracle GoldenGate.
If you want to follow me on a more timely manner, I can be followed on twitter at @dbasolved or on LinkedIn under “Bobby Curtis MBA”.


